Special Flavors of Linux

One of the important aspect of Linux is its Open Source nature: everyone is free to contribute and no one "owns" Linux. This creates a great diversity which is both a strength and a weakness for the operating system. Wars over the best "distro" of Linux are fought with religious zeal. Best known are the generalist Linux distributions, such as Debian, Ubuntu, Redhat, CentOs and Fedora for example. These distributions can be used to power anything from a desktop environments to production servers. However, other "lesser" known distributions are specialized for one task only, a task they often do exceptionally well. The following are three Linux distributions essential to my home setup.
FireWall : IpFire
Nowadays, it is very dangerous to have a computer directly connected to the Internet. Unless you know what you are doing, you can expected that computer to be taken over by an attacker in mere minutes. A firewall protects a computer by intercepting network traffic and blocking unwanted connections. In most home, this is done by a small dedicated appliance, the Internet router.
Power users can chose to operate their own router/firewall using PC hardware and specialized operating system. This has the distinct advantage of not relying on a router manufacturer for features or security updates. One such operating system is IpFire, a popular Linux firewall. It can be installed on almost any x86 hardware, assuming it has at least two Ethernet ports. Management is mostly done using a web interface, although a couple of configuration options can only be found at the command line.
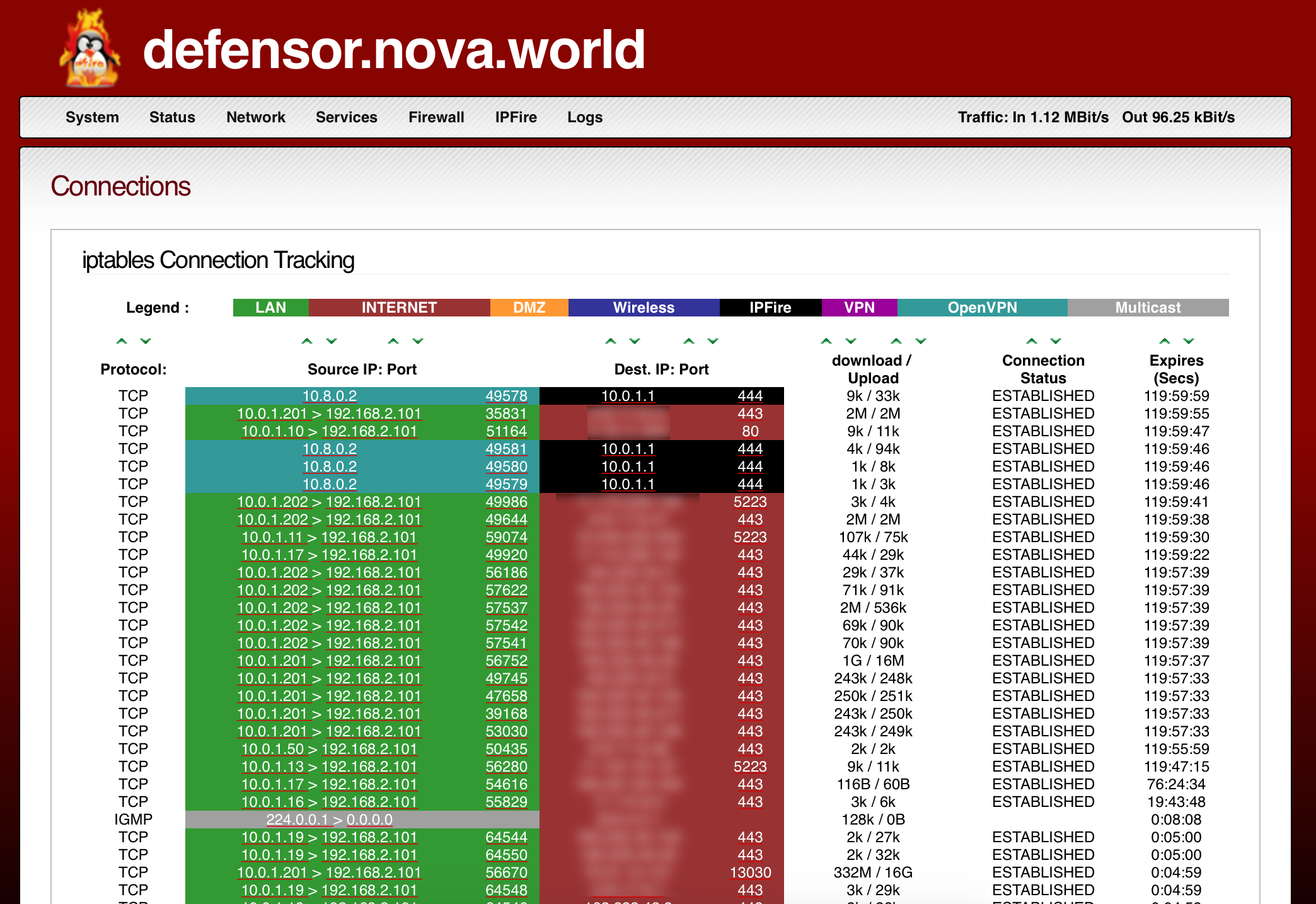
IPfire splits traffic into four categories: Internet (Red), Internal Network (Green), Wifi Network (Blue) and DMZ (Orange). IPTables can be configured to determine what traffic is allowed to cross which zone. Default rules allow computers to access the Internet ( Green and Blue can go to Red ), also protecting them ( Red can't access Green and Blue ). Machines accessible from the Internet should be in the orange zone. Typically, a network port is required for each zone. However, traffic can also be separated using VLANs.
IpFire does its job exceptionally well. However, the firewall is very constrained to the design choices of the four colors mentioned above. Understandably, this was done to keep the design simple and straight-forward to use. It also has the disadvantage that deviating from this design is very difficult and would be best done with another distribution.
Network Attached Storage : OpenMediaVault
Network Attached Storage (NAS) is having one of more hard disks accessible thought your home network. A NAS is sharable among several computers and often feature safeguards to protect data from the loss of a disk (RAID). Dedicated hardware solutions (just plug it in your network and it works) are available from both harddisk makers (Western Digital, Seagate) and specialize storage providers (Synology , Drobo, Qnap).
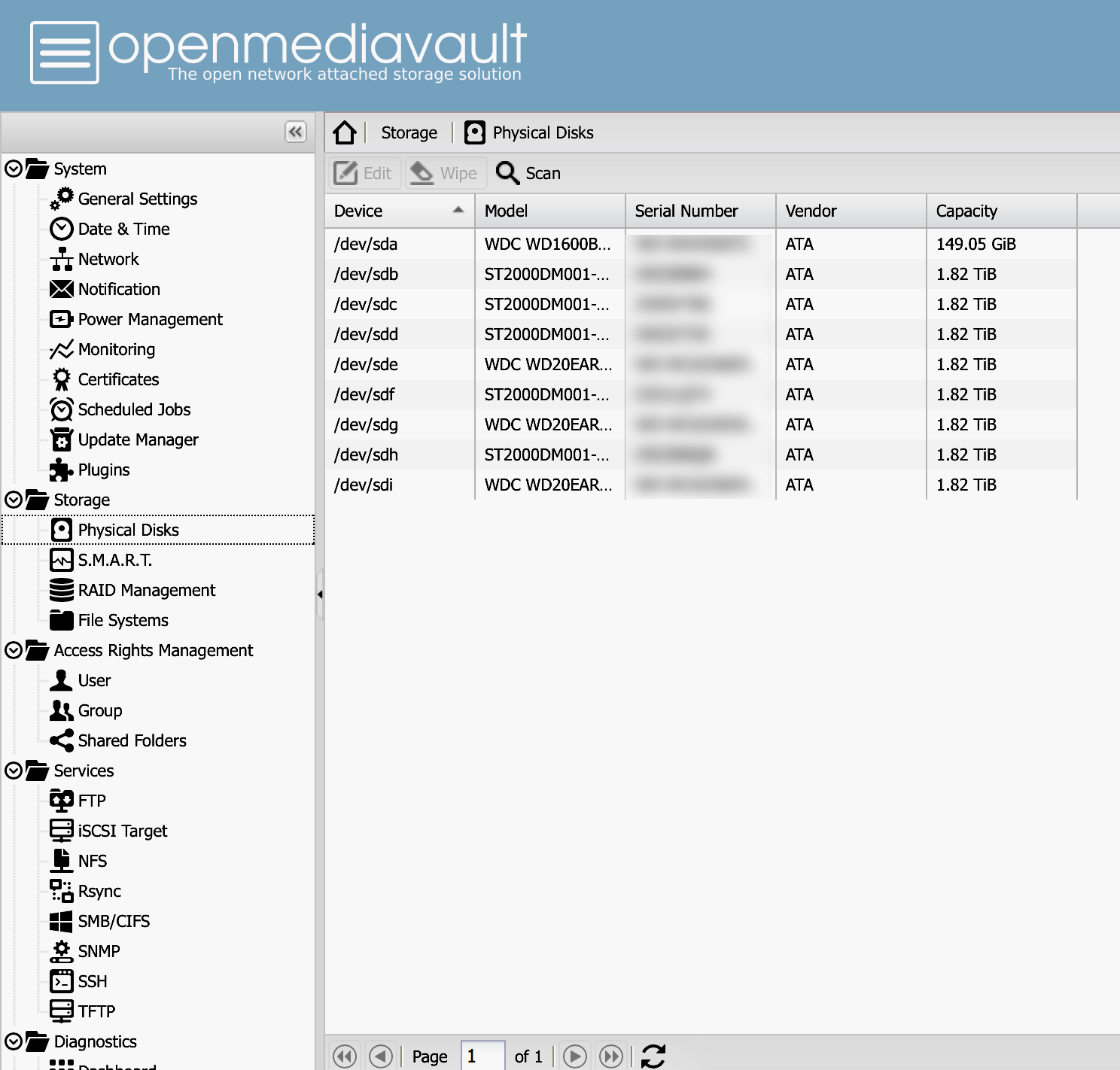
At times, you might want more flexibility than what is provided by dedicated solutions. A NAS can also be built using regular computer hardware, a bunch of hard drives and a some specialized software. In this case, FreeNAS, a variant of FreeBSD is the undisputed king of storage. For those prefering to stay within the Linux ecosystem, OpenMediaVault (OMV) is a very strong contender.
Sharing disk space can be done over several network protocols such as SMB, NFS, AFP and iSCSI, all supported by OMV. Disk redundancy is achieved through Linux's software raid solution: mdadm. Modern hard drivers can monitor their own health status through their SMART interface, which is monitored in turn by smartctl. I can not help but vouch by these tools, which have help my data survive numerous failed ( or almost failed ) hard drives.
Computers connect to the NAS by using shared points mount, which are defined in OMV's handy web interface. You can also manage permissions, or schedule some processes to be executed at regular interfaces, such as R-Sync backups.
OMV main weakness is the user management. Although the product in itself is very secure, solving problems related to permissions can be very difficult. For example, when setting up a simple SMB share, it's very important to set permissions with Samba, the file system ACL and set the proper user/group ownership. Solving "permission denied" problems can be a frustrating experience. These problems are tied to how Linux is designed and how OMV the software OMV manages are built to use it. Regardless, OMV remains a reliable file sharing platform.
Virtualisation : Proxmox
Virtualization is operating one or several virtual machines on a more powerful computer, called a hypervisor. Products like Virtual Box allow virtual machines to be easily setup on desktop computers. Operating systems for servers will often have virtualization built-in and Modern CPU are built with features to improve virtualization performance.
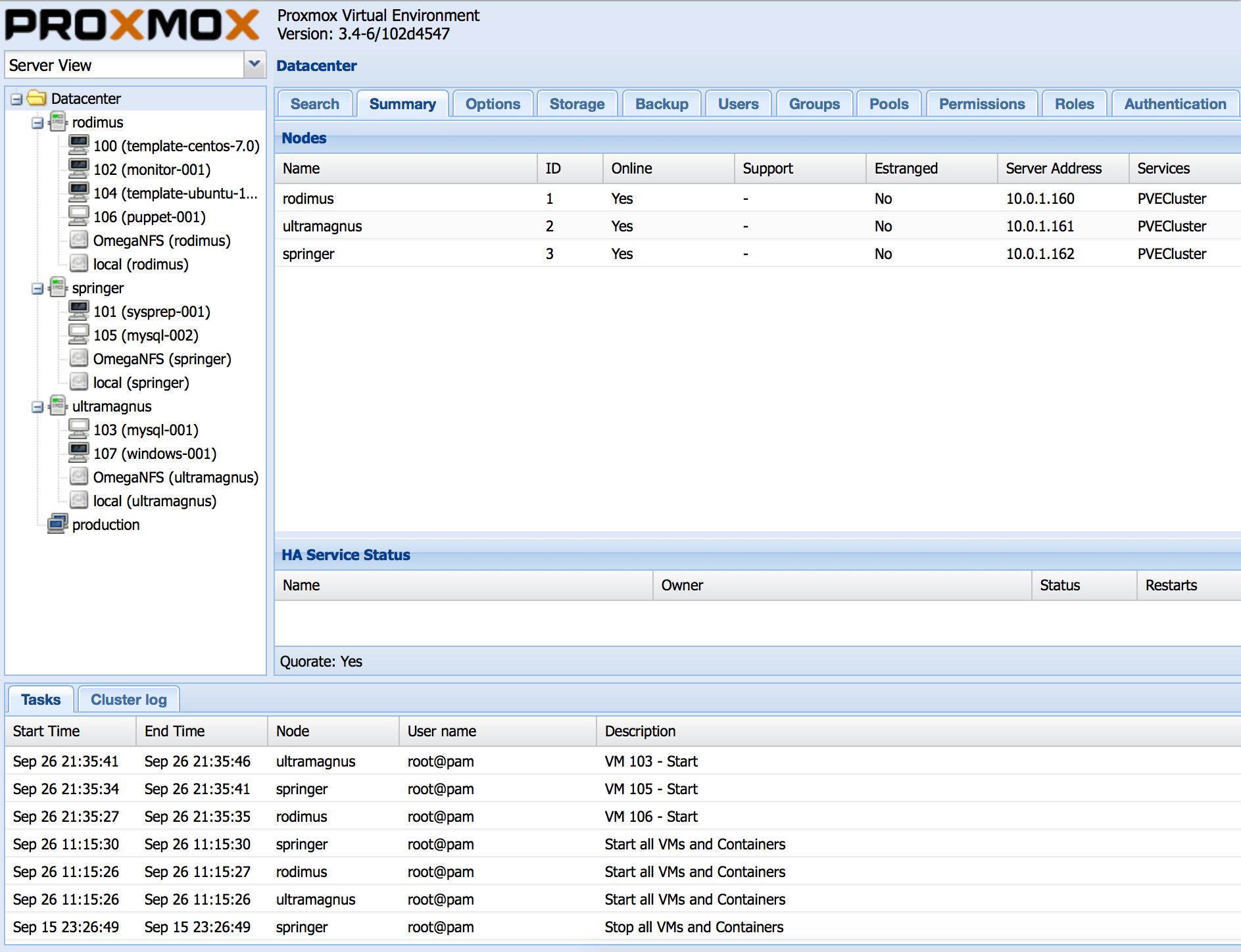
More elaborate virtualization setups will group multiple hypervisors to work together. This is called a virtualization cluster and forms the basis for a cloud infrastructure. The goal is to use the cluster as if it was one big hypervisor : new virtual machines are create on the hypervisor with less load and existing virtual machines can be redistributed in case of single hypervisor failure. Openstack is, by far, the most popular solution to implement large hypervisor clusters. On the entreprise side, VMWare provides the favoured solution at a high price. For a smaller clusters running on free software, Proxmox provides a simple solution that can easily grow with time.
Under the hood, Promox is a collection of existing open-source technologies packaged togheter with some excellent management software. A GUI interface guides the installation proceed, and creating a cluster simply requires a few commands on the command line. Creating virtual machines (VMs) is simple through the web interface. They can then be easily managed, adding resources or removing them as needed. Their consoles can be accessed using some handy web-based VNC interface. Virtual media can be uploaded to a shared pool and then shared among any number of VMs. In case of maintenance, VMs can easily be moved from one machine to another.
Error handling would be one of Proxmox's weakness. Error messages are often cryptic, if not completely absent. Although the logs can provide a bit more information, its easier to seek help on the Internet. Given the large Proxmox following, it is likely that somebody has had the same problem before and shared how to fix it. Once example would be the web-based VNC interfaces will silently fail on some browsers if the SSL certificates are not completely trusted.
Having tested and uninstalled several other free virtualization solutions such as oVirt, Kimchi and Archipel, I stand confident with Proxmox as simple solution that just work.
- Ice Cream Photo by Dirk Vorderstraße and licensed under the cc-by-2.0.




